A new U.S. class action against Circle raises a fundamental question for the digital financial system: when does a crypto infrastructure provider stop being a neutral technology layer and become legally accountable for enabling the movement of stolen assets?
A New Test Case for Crypto Infrastructure Liability
A class action complaint filed in the United States District Court for the District of Massachusetts on 14th April 2026 raises a legally significant question for victims of digital financial crime: can a crypto infrastructure provider be held liable when stolen assets are moved through its technology, while the provider allegedly has notice of what is happening and the ability to intervene?
The case was filed against Circle Internet Group, Inc. and Circle Internet Financial, LLC. According to the complaint, attackers drained approximately USD 280 million in crypto assets from Drift Protocol, a decentralized exchange on Solana, and then used Circle’s USDC stablecoin and Cross-Chain Transfer Protocol (CCTP) to move the value from Solana to Ethereum.
The core allegation is different: Circle allegedly enabled the exit route.
The case is part of a broader legal debate about whether financial and technological infrastructure providers can be held accountable when their systems allegedly help stolen value move, become concealed, or become practically unrecoverable.
The Core Argument: Notice, Control, and Failure to Act
The plaintiff’s theory is built around two legal claims: aiding and abetting conversion and negligence.
According to the complaint, the attackers first converted stolen assets into USDC, then used Circle’s CCTP bridge over approximately eight hours to move those assets from Solana to Ethereum. Once on Ethereum, the assets were allegedly converted into Ether, making them harder to freeze or recover.
The liability argument follows a simple structure:
notice + control + time to act + failure to intervene = potential liability
The complaint alleges that Circle was on notice because the exploit was publicly discussed, Drift Protocol itself confirmed an active attack, and Circle was specifically called upon to intervene. It further alleges that Circle had the ability to freeze USDC or block the use of its bridge infrastructure, but failed to do so.
At this stage, the complaint appears to rely mainly on public warnings and circumstantial evidence. It does not yet point to internal Circle communications, compliance alerts, blockchain-monitoring logs, or internal decisions not to act. Those facts would likely need to be tested through discovery.
Still, the case is legally significant because it frames Circle not as the hacker, but as an alleged infrastructure enabler of the exit route.
Why the Eight-Hour Window Matters
The alleged eight-hour bridging period is central. If the movement of stolen assets had occurred instantly, Circle could more easily argue that no meaningful intervention was possible. But the complaint alleges a longer exit phase during which warning signs were public and action was allegedly possible.
The key question is therefore not only who committed the original theft. The question is whether Circle’s infrastructure allegedly helped make the theft successful, irreversible, or unrecoverable
That is the core of modern infrastructure-liability litigation.
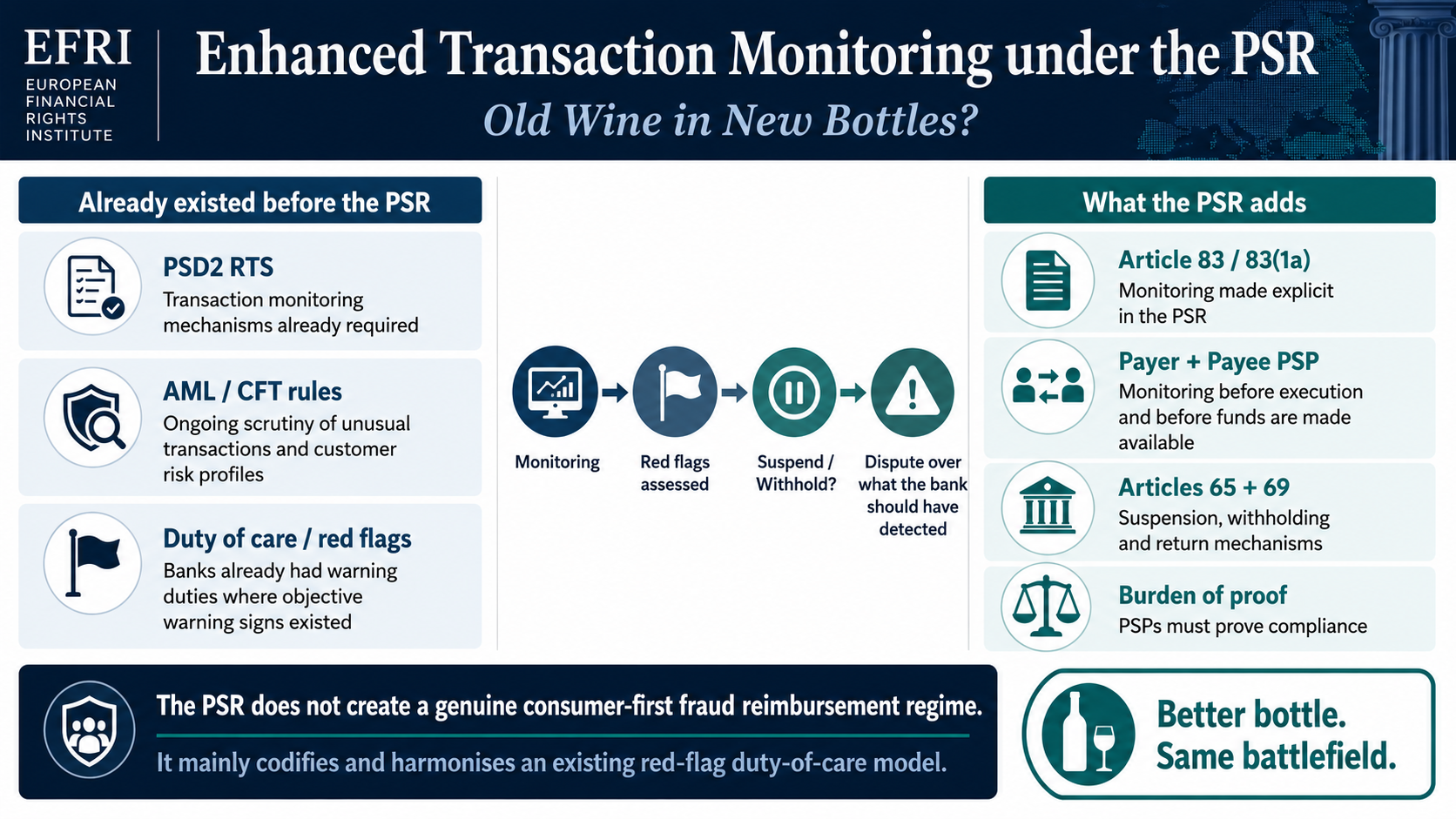
Why This Matters Beyond Crypto
The Circle case matters because it reflects a wider shift in financial crime litigation. Victims are increasingly looking beyond anonymous hackers or offshore fraudsters and asking whether identifiable infrastructure providers played a material role in moving or preserving stolen value.
The same question arises in payment-processing, merchant-acquiring, banking, crypto-exchange, and scam-advertising cases:
Was the provider merely a neutral intermediary, or did it have notice, control, and the ability to reduce harm?
The Payvision Comparison: Why EFRI Sees a Broader Pattern
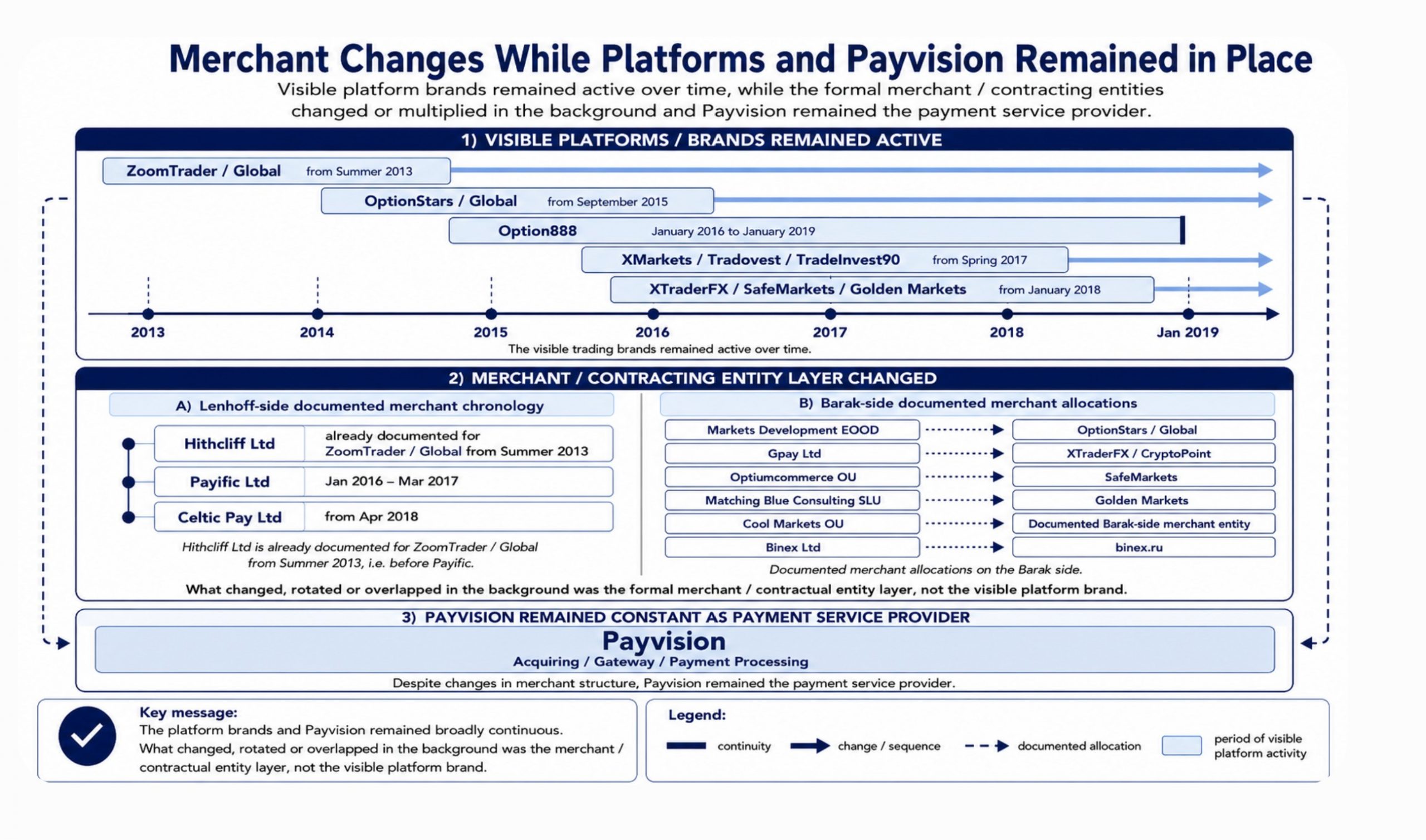
For EFRI, the Circle case is important because it mirrors a broader question raised in the Payvision matter: when does a financial infrastructure provider stop being a neutral processor and become part of the system that allows unlawful funds to move?
The Circle complaint is primarily an alleged failure-to-freeze case. It concerns one exploit and an alleged eight-hour window.
The Payvision evidence, as set out in EFRI’s Payvision Files, appears materially different. According to the dossier, Payvision’s role in the Lenhoff/Barak platform structures was not limited to isolated card processing. The files describe a multi-year pattern involving merchant structures, MID migrations, MCC classification, settlement routing, withdrawals, third-party payouts, chargeback handling, fraud reports, FIU/SAR filings, and repeated adaptation of payment routes despite escalating red flags.
In short:
Circle is pleaded as an alleged failure-to-freeze case. Payvision is documented as an alleged system-maintenance case.
That distinction matters.
In the Circle case, the plaintiff must still prove that Circle had actual or legally relevant notice, that it could realistically intervene, and that its failure caused or increased the loss.
In the Payvision matter, the central allegation is broader: Payvision allegedly helped maintain payment access over years, despite chargebacks, fraud reports, regulator warnings, bank account problems, merchant changes, and escalating risk indicators.
Notice Was Stronger in Payvision
In the Circle complaint, knowledge is largely built on public warnings and the alleged visibility of the exploit.
In the Payvision matter, the dossier points to direct institutional knowledge. It records substantial processing volumes, thousands of chargebacks and fraud reports, and 273 suspicious activity reports filed with the Dutch Financial Intelligence Unit between August 2016 and January 2019 in relation to the relevant platform structures.
That is a stronger evidentiary position. It suggests that the risk indicators were not external rumours, but part of Payvision’s own operational and compliance environment.
Control Was Broader in Payvision
Circle’s alleged control concerns its ability to freeze USDC or restrict use of CCTP.
Payvision’s alleged control points were broader: merchant onboarding, MID allocation, MCC classification, settlement routing, rolling reserves, chargeback handling, withdrawals, third-party settlements, contract continuation, and risk pricing.
The Payvision dossier describes repeated merchant transitions and continued processing despite licence issues, regulatory warnings, account problems, and high chargeback levels.
That makes the Payvision case less about a single missed intervention and more about the alleged maintenance of a payment architecture.
Conclusion
The Circle class action is still at the allegation stage. Circle has not been found liable. But the case is important because it brings a central issue into focus: infrastructure providers may face scrutiny where they allegedly have notice, control, and the ability to prevent stolen value from moving beyond recovery.
For EFRI, the broader lesson is clear. Financial crime litigation is increasingly about infrastructure. Accountability cannot stop with anonymous hackers, offshore fraudsters, or insolvent shell companies. Where identifiable infrastructure providers allegedly help stolen-value systems operate, continue, or become unrecoverable, courts will increasingly be asked whether passive non-intervention is enough or whether it can become legally actionable assistance.