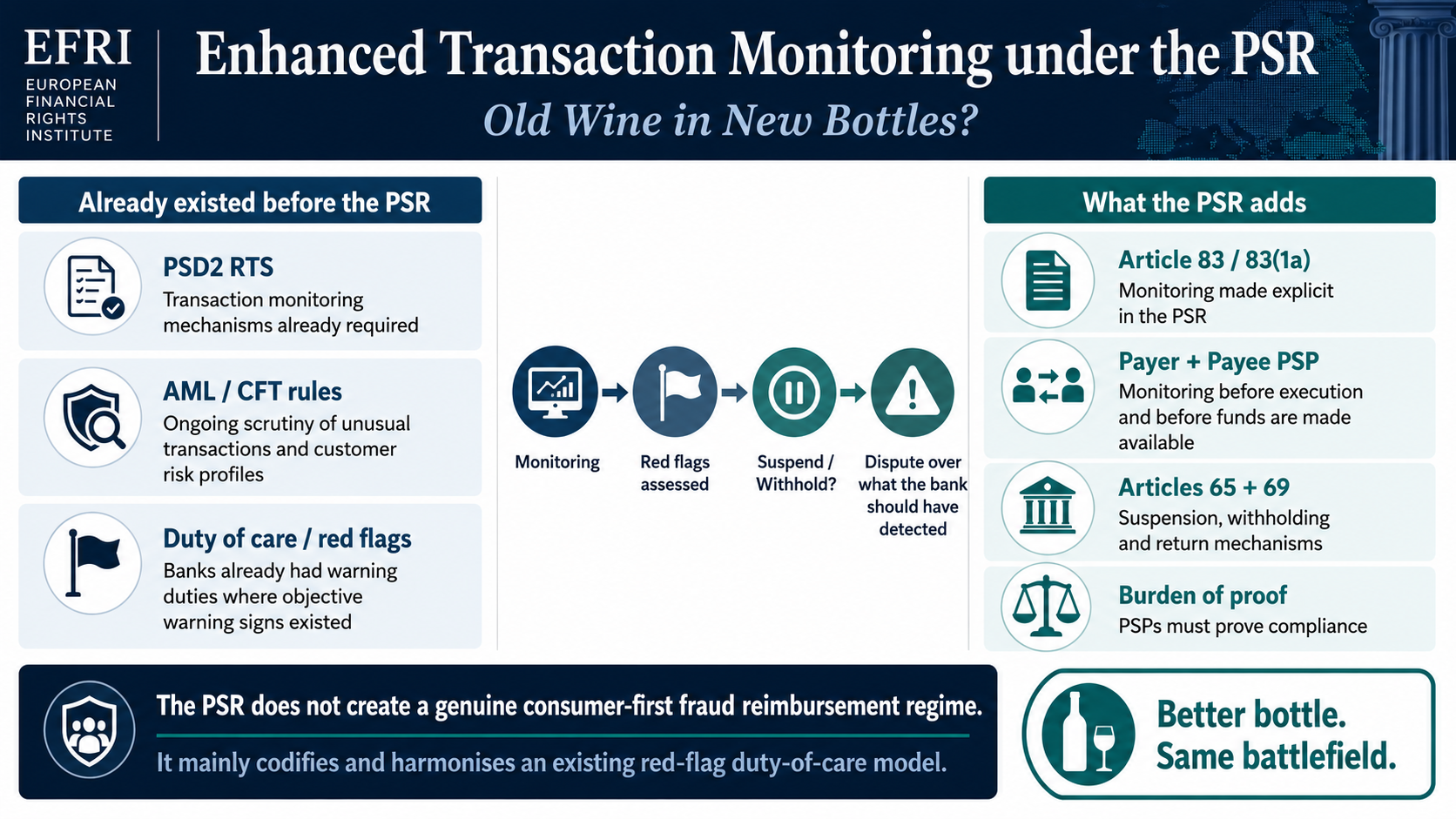
The primary purpose of scams is to obtain victims’ money.
With the “Follow the Money” approach becoming a well-known investigative tool for prosecutors, opaqueness and complexity in structuring the money flow from victims to scammers are critical for cybercriminals.
The more opaque and complex a payment method is, the more scammers love to use it.
Consumer preferences for different online payment methods also play a crucial role in any online scam’s success. People from other countries use various payment methods: Germans and Swiss people prefer to transfer higher amounts via wire transfers. British people are more accustomed to digital payments and often use their debit cards for significant transactions.
Technical Payment Service Providers (payment gateway providers) offer online shops specialised interfaces to alternative payment methods. The more different payment options a website provides, the better. Frictionlessness is for scams as crucial as it is for any other online shopping website.
With credit/debit card payments being the most widely accepted form of digital payment, the possibility of accepting card payments for their brands (scam websites) is critical to the scammers’ success. Card payments account for about 80% of the digital payment market, with Mastercard and VISA being the dominant market players.
The first payment (99% are done via card payments) of a victim has a critical role in the fraud process!
Aggressive marketing aids (like Frank Thelen and Jeff Bezos investing heavily and successfully in crypto) lure hundreds of consumers daily to cybertrading websites like option888 (one of Uwe Lenhoff’s brands) or cryptopoint (one of Gal Barak’s brands). After providing the email and the phone number in the “easy-to-do” registration process, boiler room employees posing as experienced brokers call the consumers within a few hours. These aggressive boiler room operators aim to convince inexperienced consumers to invest a small amount (€250) and undertake a test trade.
Scripts with arguments to build trust with consumers form the basis of the conversations and include statements like, “Do you think that licensed and supervised payment companies would work with us if we were not trustworthy?”
The training of boiler room employees often pays off, and hundreds of consumers give the cybertrading website a try, transferring € 250 via card payment.
Within minutes after the approval of the card payment, the transferred amount is displayed in the victim´s (fake) trading account on the fancy cybertrading website. The victim is ready to make its first highly successful trades.

The unique role of licensed payment service providers in fraud schemes.
A technical interface between the payment gateway providers and the trading and CRM software Tradologic enables this frictionless payment crediting process for card payments. It is critical to the success of fraud websites.
Victims´ bank transfers only are credited to the victim´s trading account when received by the beneficiary – which can take several days.
Using card systems for the deposits of fraud victims massively simplifies the challenge of keeping the flow of funds as opaque and anonymous as possible.
The high complexity of card payments (at least three parties are involved) and the abbreviated information displayed on card statements make it almost impossible for the injured parties to determine the money flow in the card system. This opaqueness massively reduces the need for additional layers to disguise the origin and flow of funds.
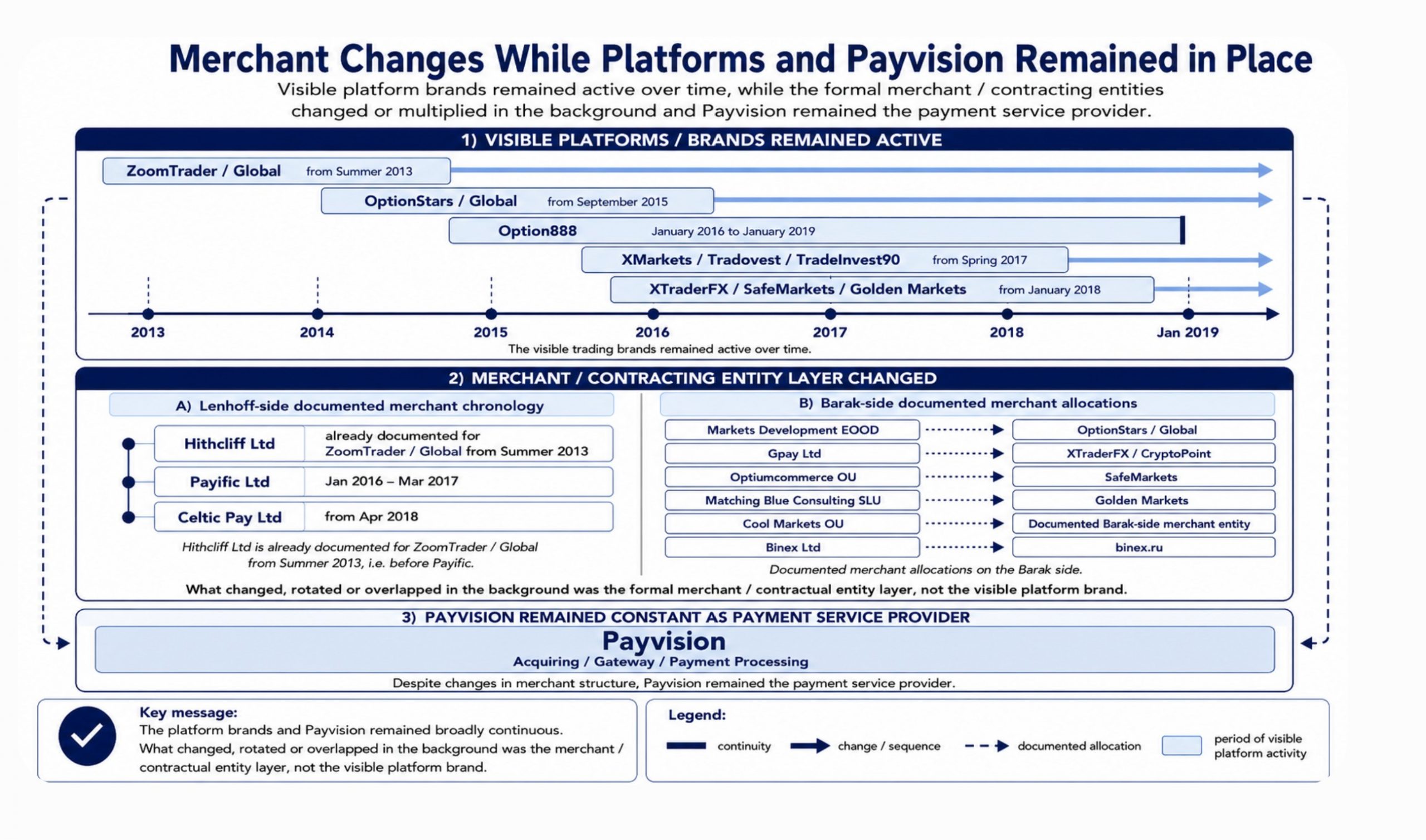
The acquirers (licensed payment institutions, such as Payvision B.V.) collect the amounts invested by the victims from the victims’ banks. The acquirers open and run separate accounts (merchant accounts) for the scams with big banks. Payvision, for example, opened bank accounts for the Barak and Lenhoff scams with Deutsche Bank and ING Bank N.V. On a biweekly basis, Payvision B.V. transferred the collected money to the bank accounts of the onboarded merchants (shell companies administered by the scammers).

The required money laundering effort of the criminal organisation, led by Gal Barak and Uwe Lenhoff, was thus significantly reduced through cooperation with licensed payment institutions, such as Payvision B.V.
Compared to the requirements of countless shell companies that have to be equipped with bank accounts, which regularly result in bank accounts being blocked after several weeks (compare below), the payment institutions provide a collective account through which tens of millions of euros can flow to the same shell company (contractual partner) over several years. Payvision, for example, worked with them from 2014 to 2019 without any serious issues.
This reduction in complexity for the fraudsters is being handsomely rewarded by the credit card companies working for the fraudsters.
Increased challenges coming with bank deposits
Victims from Western European countries prefer to use wire transfers for higher deposits. Therefore, the victim receives the data for the transfer (the beneficiary bank account number) via email from the boiler room employees.
Within the industry, the structuring of the intake of victims’ money and the required money laundering to disguise the origin of the funds are offered as a service by sophisticated money laundering organisations. They provide the service for the intake and the transfer of victims´ money with several layers. Paul Lopatin, sentenced to four years in jail for money laundering in Germany in 2020, managed more than 40 different bank accounts (mainly with Postbank) for approximately in 2018 and 2019.
Multiple layers must be used to disguise the money flow and offset the increased transparency of bank transfers. The money was transferred using sham contracts (loan consultancy contracts) over several (usually three) levels (in each case, shell companies with collective accounts at European banks in other countries) to disguise the criminal origin of the money as much as possible. Each additional level (bank accounts of another shell company) represented a further layer of laundering for the money or the money flow.
One of the principles of money laundering in this context is that the concealment becomes more successful with each washing cycle (layer). In most cases, integration occurs at the second level; the origin of the funds can no longer be determined, and the “laundered” money is used as if it originated from legitimate business activities.
But with the life of these (collection points for the money) bank accounts being usually limited to a few months, the advantage of a long-term merchant account with an acquirer is evident. When the first victims realize the fraud, they contact their “home” bank and request a chargeback of the transferred amount. The home banks must investigate, inform their correspondent banks about the suspected fraud, and flag identified fraud accounts. Within a few weeks, the funds are blocked, and new shell companies with new collective accounts must be provided in parallel. This can not happen with a merchant account.
Example: ING bank accounts were used for Barak and Lenhoff's fraud organizations
ING Bank N.V. was also used by international fraud and money laundering organisations, including those led by Gal Barak and Uwe Lenhoff, to receive funds from fraud victims and facilitate the subsequent transfer of the funds across multiple layers, ultimately into the personal control of Gal Barak and Uwe Lenhoff.
MoneyNetInt Ltd, London – an e-money and payment institution licensed by the Financial Conduct Authority (FCA) (reference number 900190) – had an account with “L’ski polnische ING Bank Spéka Akcyjna” (PL73105000861000009030701412). The bank account was used for deposits of the victims of the scam website, optionstarsglobal
As early as July 2016, the Times of Israel reported MoneyNetInt’s involvement in binary options fraud. In spring 2017, the Polish Financial Supervision Authority (“KNF”) issued a warning regarding the activities of MoneyNetInLtd.
Leonsky Ltd. in Madrid, Spain, held an omnibus account with the Spanish ING Bank SUCURSAL EN ESPANA (ES17 1465 0100 9519 0060 4045). This account was also used for Gal Barak’s fraud schemes
ING’s German subsidiary in Frankfurt provided ICEPAY B.V., Amsterdam, with an account (DE88 5002 1000 0010 1193 45). The company was used to transfer stolen funds for Lenhoff’s fraud platform.
Additional services of the licensed PSP!
Acquirers like Payvision also did some other jobs for criminal organizations.
Ponzi-Refunds
By the instruction of the criminal organisations, Payvision assisted in making Ponzi refunds via credit entries to the credit card data of individual victims. These disbursed profits (Ponzi payments) are used as a lure for further deposits. Here, the fraud schemes also take advantage of the lack of transparency of the card systems, so that only the website’s name appears on the credit card statement. As in the case of deposits into the fraud system, it is unclear to the individual customer which payment institution or credit institution carries out the debit or credit entry on behalf of the fraud platforms and which company credited the amount.
Money transfers to Lenhoff and Barak
At the request of Uwe Lenhoff and Gal Barak, Payvision B.V. also transferred several million victims’ money to bank accounts of the beneficial owners, although neither Lenhoff nor Gal Barak appeared as managing directors or beneficial owners of the contracting party of Payvision B.V.
Cooperation in reducing of charge-back requests and fraud complaints
If the period within which the victim can request a refund of their deposits from their credit company has expired, the risk of a claim against the credit card companies to date is minimal.
Nevertheless, the high number of chargeback requests (even after the deadlines have expired) poses a significant problem for credit card companies in their fraud systems, as credit card organisations are particularly likely to impose high penalties if predefined chargeback quotas are exceeded.
However, techniques such as using several different shell companies (merchants) chronologically or in parallel for the same fraud platform and using false Merchant Category Codes (MCC) cleverly limit the risk.
The frictionless process of the first credit card transaction and the apparent professionalism of the website, in combination with the manipulative calls of the call center employees, resulted in up to six-figure losses for the victims.